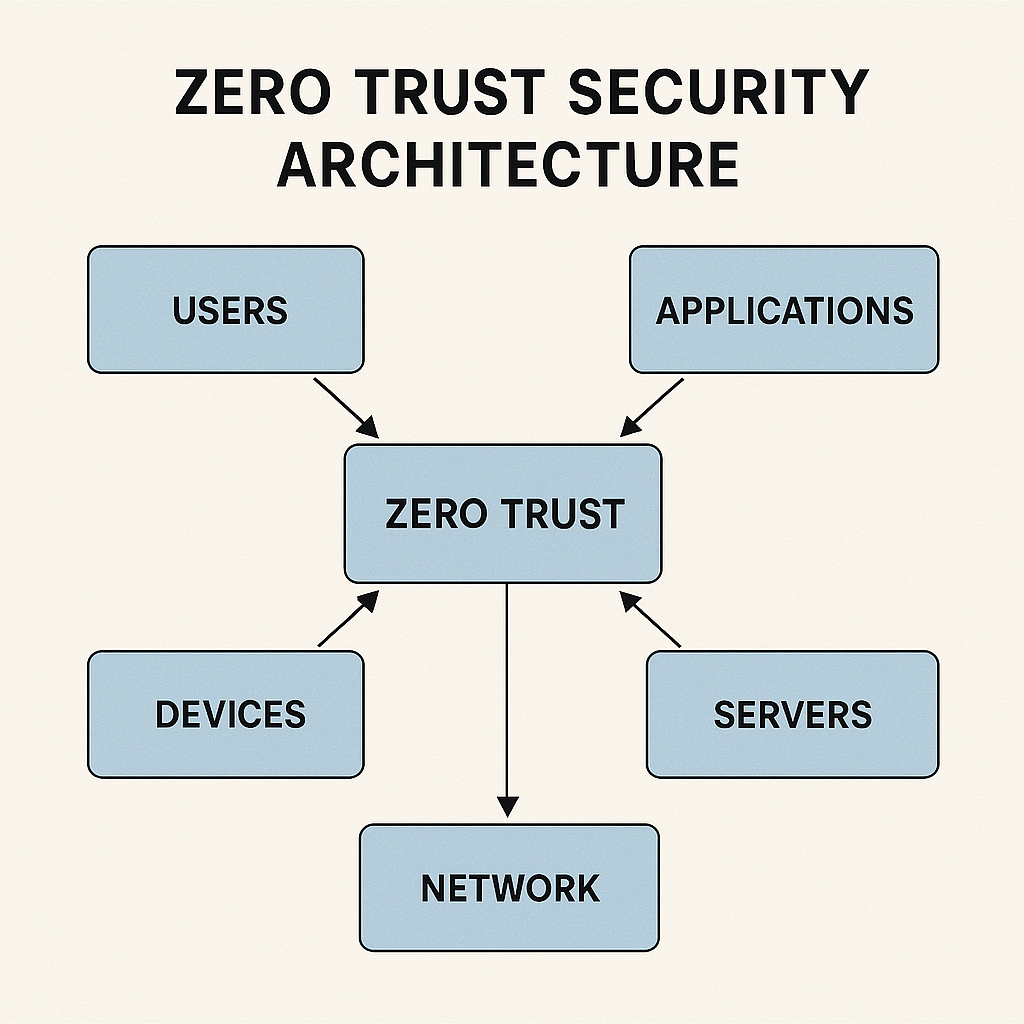
Zero Trust Security Architecture is a modern cybersecurity model built around the principle “Never Trust, Always Verify.” Unlike traditional security systems that trust internal networks and users by default, Zero Trust assumes that every user, device, network connection, or application is potentially unsafe until proven otherwise. With rising cyber threats, remote work, multi-cloud environments, and sophisticated hacking techniques, organizations can no longer rely on perimeter-based security. Zero Trust provides continuous verification, strict access control, and strong identity management to protect data regardless of location.
Cyberattacks have evolved far beyond simple malware or phishing attempts. Today’s attackers use insider threats, stolen credentials, supply chain breaches, ransomware, and lateral movement inside networks. Traditional firewalls and VPN systems cannot protect against attackers once they gain access. Zero Trust minimizes this risk by removing implicit trust. Every request—whether internal or external—is verified, monitored, and validated in real-time. This reduces attack surfaces and ensures only authenticated, authorized, and healthy devices can access sensitive data.
Zero Trust is built on three main principles:
1)Verify Explicitly – Always authenticate and authorize based on identity, device, location, and behavior.
2)Use Least-Privilege Access – Give users only the permissions they absolutely need.
3)Assume Breach – Design systems assuming attackers are already inside and limit their movement.
These principles form the foundation of Zero Trust and help create a safer, more controlled security environment.
Zero Trust is not a single tool but a combination of multiple security layers:
1)Identity and Access Management (IAM)
2)Multi-Factor Authentication (MFA)
3)Endpoint Security & Device Posture Checks
4)Network Micro-Segmentation
5)Least-Privilege Policies
6)Real-Time Monitoring & Logging
7)Data Encryption at Rest and In Transit
These components work together to verify every request, restrict access, and detect suspicious activity before it becomes a threat.
Here is a simple workflow of how Zero Trust operates:
🔹 Step 1: User or Device Requests Access
A user logs in or a device tries to access a network resource.
🔹 Step 2: Identity Verification
The system checks username, password, MFA, biometrics, and identity tokens.
🔹 Step 3: Device Health Check
It verifies device status—OS updates, antivirus, location, IP address, risk score.
🔹 Step 4: Access Policies Applied
Based on user role + device trust + behavior, the system decides what can be accessed.
🔹 Step 5: Micro-Segmented Access
The user is only allowed to access specific applications—not the entire network.
🔹 Step 6: Continuous Monitoring
User behavior and access patterns are tracked for threats.
🔹 Step 7: Automatic Block if Risk Detected
If unusual activity occurs, the system blocks access instantly,This makes Zero Trust powerful, secure, and highly reliable.
The Zero Trust model offers powerful advantages:
1)Stops lateral movement of attackers
2)Reduces risk of data breaches
3)Improves visibility across users and devices
4)Supports secure remote work
5)Protects cloud workloads and APIs
6)Enhances regulatory compliance (GDPR, HIPAA, PCI)
7)Reduces insider threat risks
These benefits strengthen the security posture of any organization, big or small.
Despite its advantages, Zero Trust implementation can be challenging. Organizations must update legacy systems, migrate to modern IAM platforms, redesign network segmentation, deploy MFA across users, create detailed access policies, and train employees to adapt to new systems. Integration across cloud platforms, on-premise systems, and mobile devices requires planning and expert support. However, once implemented, Zero Trust drastically improves overall security and reduces long-term cyber risks.
Various industries are adopting Zero Trust rapidly.
1)Finance uses Zero Trust to protect customer data and prevent fraud.
2)Healthcare secures medical records, devices, and remote telehealth platforms.
3)E-commerce prevents account takeover attacks and secures payment gateways.
4)Government and defense rely on Zero Trust for high-level intelligence protection.
5)Enterprises use it to secure cloud apps, remote employees, and large-scale operations.
Its flexibility makes it ideal for any organization prioritizing security.
The future of Zero Trust is closely tied to AI, automation, and behavioral analytics. AI-powered Zero Trust systems will monitor patterns, detect anomalies, and enforce policies automatically. Cloud-native Zero Trust and Zero Trust for IoT, 5G, and Edge networks will also grow rapidly. As cyber threats become more advanced, Zero Trust will evolve from an option to a global security standard.
Cyberattacks have evolved far beyond simple malware or phishing attempts. Today’s attackers use insider threats, stolen credentials, supply chain breaches, ransomware, and lateral movement inside networks. Traditional firewalls and VPN systems cannot protect against attackers once they gain access. Zero Trust minimizes this risk by removing implicit trust. Every request—whether internal or external—is verified, monitored, and validated in real-time. This reduces attack surfaces and ensures only authenticated, authorized, and healthy devices can access sensitive data.
Zero Trust is built on three main principles:
1)Verify Explicitly – Always authenticate and authorize based on identity, device, location, and behavior.
2)Use Least-Privilege Access – Give users only the permissions they absolutely need.
3)Assume Breach – Design systems assuming attackers are already inside and limit their movement.
These principles form the foundation of Zero Trust and help create a safer, more controlled security environment.
Zero Trust is not a single tool but a combination of multiple security layers:
1)Identity and Access Management (IAM)
2)Multi-Factor Authentication (MFA)
3)Endpoint Security & Device Posture Checks
4)Network Micro-Segmentation
5)Least-Privilege Policies
6)Real-Time Monitoring & Logging
7)Data Encryption at Rest and In Transit
These components work together to verify every request, restrict access, and detect suspicious activity before it becomes a threat.
Here is a simple workflow of how Zero Trust operates:
🔹 Step 1: User or Device Requests Access
A user logs in or a device tries to access a network resource.
🔹 Step 2: Identity Verification
The system checks username, password, MFA, biometrics, and identity tokens.
🔹 Step 3: Device Health Check
It verifies device status—OS updates, antivirus, location, IP address, risk score.
🔹 Step 4: Access Policies Applied
Based on user role + device trust + behavior, the system decides what can be accessed.
🔹 Step 5: Micro-Segmented Access
The user is only allowed to access specific applications—not the entire network.
🔹 Step 6: Continuous Monitoring
User behavior and access patterns are tracked for threats.
🔹 Step 7: Automatic Block if Risk Detected
If unusual activity occurs, the system blocks access instantly,This makes Zero Trust powerful, secure, and highly reliable.
The Zero Trust model offers powerful advantages:
1)Stops lateral movement of attackers
2)Reduces risk of data breaches
3)Improves visibility across users and devices
4)Supports secure remote work
5)Protects cloud workloads and APIs
6)Enhances regulatory compliance (GDPR, HIPAA, PCI)
7)Reduces insider threat risks
These benefits strengthen the security posture of any organization, big or small.
Despite its advantages, Zero Trust implementation can be challenging. Organizations must update legacy systems, migrate to modern IAM platforms, redesign network segmentation, deploy MFA across users, create detailed access policies, and train employees to adapt to new systems. Integration across cloud platforms, on-premise systems, and mobile devices requires planning and expert support. However, once implemented, Zero Trust drastically improves overall security and reduces long-term cyber risks.
Various industries are adopting Zero Trust rapidly.
1)Finance uses Zero Trust to protect customer data and prevent fraud.
2)Healthcare secures medical records, devices, and remote telehealth platforms.
3)E-commerce prevents account takeover attacks and secures payment gateways.
4)Government and defense rely on Zero Trust for high-level intelligence protection.
5)Enterprises use it to secure cloud apps, remote employees, and large-scale operations.
Its flexibility makes it ideal for any organization prioritizing security.
The future of Zero Trust is closely tied to AI, automation, and behavioral analytics. AI-powered Zero Trust systems will monitor patterns, detect anomalies, and enforce policies automatically. Cloud-native Zero Trust and Zero Trust for IoT, 5G, and Edge networks will also grow rapidly. As cyber threats become more advanced, Zero Trust will evolve from an option to a global security standard.
