Web security is the foundation of safe browsing for users and secure operations for businesses. Every website that collects or processes data—whether it’s user login details, payment information, or personal messages—must be protected. Without proper security measures, cybercriminals can easily intercept data, impersonate users, or take control of entire systems. As digital applications grow, so does the sophistication of cyberattacks. Web security fundamentals such as HTTPS, SSL/TLS encryption, and awareness of common web attacks are essential for protecting data, ensuring trust, and maintaining the integrity of online systems. Understanding these basics helps developers build safer websites and helps users interact confidently with online services.
HTTPS (HyperText Transfer Protocol Secure) is the secure version of HTTP. The “S” represents security, achieved through encryption. When you browse a website with HTTPS, all communication between your browser and the server is encrypted so no third party can read or modify it. The browser displays a padlock icon in the URL bar to indicate the connection is secure. HTTPS uses the TLS (Transport Layer Security) protocol to encrypt data. This ensures confidentiality (data cannot be read by attackers), integrity (data cannot be changed without detection), and authentication (the website you visit is genuine). Today, all major browsers mark non-HTTPS websites as “Not Secure,” making HTTPS not just recommended but mandatory.
SSL (Secure Sockets Layer) is the older encryption technology, now replaced by TLS (Transport Layer Security). People still commonly refer to “SSL certificates,” but technically websites use TLS today. An SSL/TLS certificate is a digital document issued by a trusted Certificate Authority (CA) such as DigiCert or Let’s Encrypt. It verifies the website’s identity and establishes an encrypted connection using public-key cryptography. When a browser connects to a website, it performs an SSL/TLS handshake—exchanging keys—before sending encrypted data. This protects sensitive information like passwords, credit card numbers, and personal data. Without SSL/TLS, attackers can intercept communications and steal or modify data through attacks such as Man-in-the-Middle (MITM).
SSL/TLS certificates contain a website’s public key, domain name, issuer details, expiration date, and digital signature. When you visit a site, this certificate is sent to your browser, which then validates it using the CA's public key. If the certificate is valid, trusted, and not expired, the browser establishes a secure session using symmetric encryption for fast communication. Certificates come in different types—Domain Validation (DV), Organization Validation (OV), and Extended Validation (EV)—each offering different levels of trust. EV certificates, for example, undergo strict verification and were traditionally used by banks and e-commerce companies. Regardless of type, the purpose remains the same: to prove identity and encrypt communication.
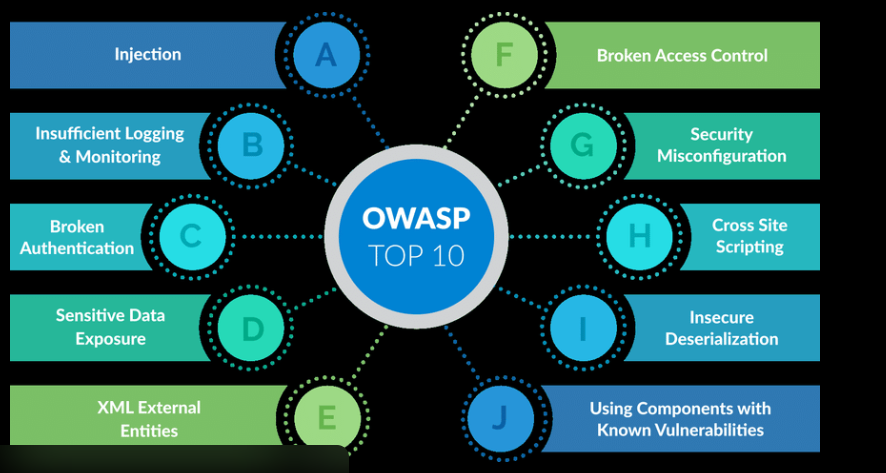
Even with HTTPS and SSL/TLS, websites must defend against common cyberattacks. XSS (Cross-Site Scripting) occurs when attackers inject malicious scripts into webpages to steal information or hijack sessions. SQL Injection (SQLi) targets databases, allowing attackers to access or delete sensitive data through manipulated input fields. CSRF (Cross-Site Request Forgery) tricks authenticated users into performing unwanted actions, such as changing passwords or transferring funds. Brute-force attacks involve automated attempts to crack passwords. Directory traversal attacks exploit poorly configured servers to access restricted files. Recognizing these attacks helps developers implement proper validations, secure coding practices, and defensive mechanisms.
A Man-in-the-Middle (MITM) attack happens when an attacker secretly intercepts communication between a user and a website. This allows them to read, modify, or steal data. MITM attacks typically occur on public Wi-Fi networks or insecure HTTP connections. HTTPS with SSL/TLS prevents MITM attacks by encrypting traffic, making it unreadable even if intercepted. Additionally, security features like HSTS (HTTP Strict Transport Security) force browsers to always use HTTPS, preventing downgrade attacks where hackers try to trick users into using an insecure connection. Modern browsers also implement certificate pinning to ensure the website’s identity cannot be spoofed.
To protect websites from attacks, developers must follow essential best practices. These include input validation, escaping user input, sanitizing data, and using parameterized queries to prevent SQL injection. Strong authentication measures such as password hashing, multi-factor authentication, and secure session management are critical. Regular security audits, penetration testing, and vulnerability scanning using tools like OWASP ZAP or Burp Suite help detect weaknesses early. Implementing rate limiting prevents bots from triggering brute-force attacks, while CORS policies secure cross-domain communication. Secure configuration of servers, firewalls, content security policies, and continuous monitoring ensures ongoing protection.
A Web Application Firewall (WAF) acts as a filter between web applications and the internet. It inspects incoming traffic and blocks malicious requests before they reach the server. WAFs help protect against common threats like XSS, SQL injection, file inclusion attacks, and abnormal traffic spikes. They are used widely in cloud platforms like AWS, Cloudflare, and Google Cloud. Modern WAFs use machine learning to detect suspicious behavior and adapt to new attack patterns. Using a WAF increases protection without requiring changes to the website’s code, making it a valuable security layer for businesses of all sizes.
Web security is evolving rapidly with the rise of AI-based threat detection, automated monitoring systems, and zero-trust architecture. AI-powered tools can analyze large volumes of traffic and identify anomalies instantly. Zero-trust models assume that no user or system is inherently trusted, requiring continuous authorization and authentication. Encryption standards are also advancing, with TLS 1.3 offering faster and more secure handshakes. The future will include deeper integration of hardware-based security, biometric authentication, and fully automated vulnerability detection. As cyberattacks become more complex, businesses must adopt modern security frameworks to protect data and maintain user trust.
HTTPS (HyperText Transfer Protocol Secure) is the secure version of HTTP. The “S” represents security, achieved through encryption. When you browse a website with HTTPS, all communication between your browser and the server is encrypted so no third party can read or modify it. The browser displays a padlock icon in the URL bar to indicate the connection is secure. HTTPS uses the TLS (Transport Layer Security) protocol to encrypt data. This ensures confidentiality (data cannot be read by attackers), integrity (data cannot be changed without detection), and authentication (the website you visit is genuine). Today, all major browsers mark non-HTTPS websites as “Not Secure,” making HTTPS not just recommended but mandatory.
SSL (Secure Sockets Layer) is the older encryption technology, now replaced by TLS (Transport Layer Security). People still commonly refer to “SSL certificates,” but technically websites use TLS today. An SSL/TLS certificate is a digital document issued by a trusted Certificate Authority (CA) such as DigiCert or Let’s Encrypt. It verifies the website’s identity and establishes an encrypted connection using public-key cryptography. When a browser connects to a website, it performs an SSL/TLS handshake—exchanging keys—before sending encrypted data. This protects sensitive information like passwords, credit card numbers, and personal data. Without SSL/TLS, attackers can intercept communications and steal or modify data through attacks such as Man-in-the-Middle (MITM).
SSL/TLS certificates contain a website’s public key, domain name, issuer details, expiration date, and digital signature. When you visit a site, this certificate is sent to your browser, which then validates it using the CA's public key. If the certificate is valid, trusted, and not expired, the browser establishes a secure session using symmetric encryption for fast communication. Certificates come in different types—Domain Validation (DV), Organization Validation (OV), and Extended Validation (EV)—each offering different levels of trust. EV certificates, for example, undergo strict verification and were traditionally used by banks and e-commerce companies. Regardless of type, the purpose remains the same: to prove identity and encrypt communication.
Even with HTTPS and SSL/TLS, websites must defend against common cyberattacks. XSS (Cross-Site Scripting) occurs when attackers inject malicious scripts into webpages to steal information or hijack sessions. SQL Injection (SQLi) targets databases, allowing attackers to access or delete sensitive data through manipulated input fields. CSRF (Cross-Site Request Forgery) tricks authenticated users into performing unwanted actions, such as changing passwords or transferring funds. Brute-force attacks involve automated attempts to crack passwords. Directory traversal attacks exploit poorly configured servers to access restricted files. Recognizing these attacks helps developers implement proper validations, secure coding practices, and defensive mechanisms.
A Man-in-the-Middle (MITM) attack happens when an attacker secretly intercepts communication between a user and a website. This allows them to read, modify, or steal data. MITM attacks typically occur on public Wi-Fi networks or insecure HTTP connections. HTTPS with SSL/TLS prevents MITM attacks by encrypting traffic, making it unreadable even if intercepted. Additionally, security features like HSTS (HTTP Strict Transport Security) force browsers to always use HTTPS, preventing downgrade attacks where hackers try to trick users into using an insecure connection. Modern browsers also implement certificate pinning to ensure the website’s identity cannot be spoofed.
To protect websites from attacks, developers must follow essential best practices. These include input validation, escaping user input, sanitizing data, and using parameterized queries to prevent SQL injection. Strong authentication measures such as password hashing, multi-factor authentication, and secure session management are critical. Regular security audits, penetration testing, and vulnerability scanning using tools like OWASP ZAP or Burp Suite help detect weaknesses early. Implementing rate limiting prevents bots from triggering brute-force attacks, while CORS policies secure cross-domain communication. Secure configuration of servers, firewalls, content security policies, and continuous monitoring ensures ongoing protection.
A Web Application Firewall (WAF) acts as a filter between web applications and the internet. It inspects incoming traffic and blocks malicious requests before they reach the server. WAFs help protect against common threats like XSS, SQL injection, file inclusion attacks, and abnormal traffic spikes. They are used widely in cloud platforms like AWS, Cloudflare, and Google Cloud. Modern WAFs use machine learning to detect suspicious behavior and adapt to new attack patterns. Using a WAF increases protection without requiring changes to the website’s code, making it a valuable security layer for businesses of all sizes.
Web security is evolving rapidly with the rise of AI-based threat detection, automated monitoring systems, and zero-trust architecture. AI-powered tools can analyze large volumes of traffic and identify anomalies instantly. Zero-trust models assume that no user or system is inherently trusted, requiring continuous authorization and authentication. Encryption standards are also advancing, with TLS 1.3 offering faster and more secure handshakes. The future will include deeper integration of hardware-based security, biometric authentication, and fully automated vulnerability detection. As cyberattacks become more complex, businesses must adopt modern security frameworks to protect data and maintain user trust.
