The TCP/IP protocol suite is the backbone of the internet, defining how devices communicate across diverse networks. TCP/IP stands for Transmission Control Protocol / Internet Protocol, and it is responsible for establishing connections, routing data packets, and ensuring reliable delivery. IP handles addressing and routing, while TCP ensures that the data arrives correctly, without loss or duplication. This layered design allows systems built on different hardware and operating systems to communicate seamlessly.
IP (Internet Protocol) works at the network layer, assigning a unique IP address to each device, similar to a postal address. When data travels across the internet, IP divides it into packets and forwards them through different routers based on destination addresses. However, IP alone does not guarantee delivery. Packets may be lost or arrive out of order due to network congestion. This is why TCP plays a crucial role.
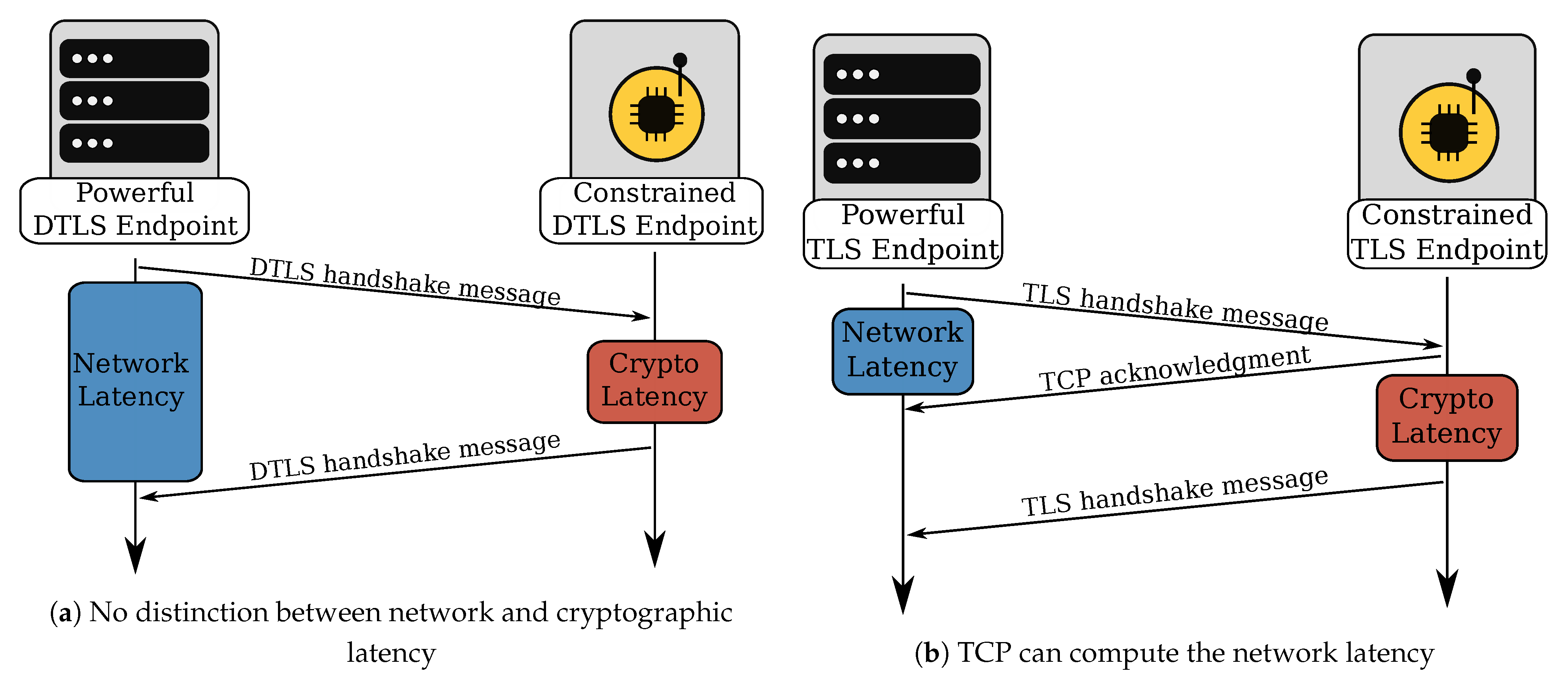
TCP functions at the transport layer and ensures reliable communication. It uses a method called Three-Way Handshake to establish a connection between sender and receiver. The handshake exchanges SYN (synchronize) and ACK (acknowledge) messages to verify that both sides are ready to communicate. Once the connection is established, TCP continuously manages packet numbering, retransmission of lost packets, and flow control to maintain stable communication. This reliability makes TCP ideal for applications like web browsing, banking, and emails.
However, TCP/IP alone is not secure. Any data sent is readable by attackers if intercepted. That is where TLS (Transport Layer Security) becomes essential. TLS is a cryptographic protocol that provides confidentiality, integrity, and authentication, ensuring data is encrypted and cannot be tampered with or viewed by unauthorized users. Websites that use TLS are identified by HTTPS instead of HTTP and show a lock icon in browsers.
The TLS handshake is a process that happens before secure communication begins. It establishes an encrypted connection between the browser (client) and the server. During the handshake, the client requests a secure connection, and the server responds with its SSL/TLS certificate issued by a trusted Certificate Authority (CA). The certificate contains the server’s public key, which the client verifies to ensure authenticity—preventing impersonation or phishing attacks.
Once authenticated, both sides negotiate cryptographic parameters—such as the version of TLS and cipher suites—to define how encryption will work. The client then generates a random symmetric encryption key (called a session key) and encrypts it with the server’s public key. Only the server’s private key can decrypt it, ensuring the key exchange remains secure. This session key is used for fast two-way encrypted communication during the session.
After key exchange, the connection moves from handshake mode to encrypted data transmission mode. Now, every message is encrypted before sending and decrypted when received. TLS also includes mechanisms to verify that the data isn’t altered during transmission—this protects against Man-in-the-Middle (MITM) attacks and data tampering. If any suspicious modifications are detected, the connection is immediately terminated.
Together, TCP/IP ensures reliable delivery, while TLS ensures security. Without these technologies working hand-in-hand, secure e-commerce transactions, online banking, private messaging, and protected personal data exchange would not be possible. Today, nearly all major websites adopt HTTPS by default because user privacy and data security have become top priorities.
In summary, TCP/IP provides the underlying structure for communication, and TLS builds on top to ensure that communication is private and trusted. Understanding how both work together is essential for web developers, network engineers, and cybersecurity professionals, as they form the core of secure internet communication.
IP (Internet Protocol) works at the network layer, assigning a unique IP address to each device, similar to a postal address. When data travels across the internet, IP divides it into packets and forwards them through different routers based on destination addresses. However, IP alone does not guarantee delivery. Packets may be lost or arrive out of order due to network congestion. This is why TCP plays a crucial role.
TCP functions at the transport layer and ensures reliable communication. It uses a method called Three-Way Handshake to establish a connection between sender and receiver. The handshake exchanges SYN (synchronize) and ACK (acknowledge) messages to verify that both sides are ready to communicate. Once the connection is established, TCP continuously manages packet numbering, retransmission of lost packets, and flow control to maintain stable communication. This reliability makes TCP ideal for applications like web browsing, banking, and emails.
However, TCP/IP alone is not secure. Any data sent is readable by attackers if intercepted. That is where TLS (Transport Layer Security) becomes essential. TLS is a cryptographic protocol that provides confidentiality, integrity, and authentication, ensuring data is encrypted and cannot be tampered with or viewed by unauthorized users. Websites that use TLS are identified by HTTPS instead of HTTP and show a lock icon in browsers.
The TLS handshake is a process that happens before secure communication begins. It establishes an encrypted connection between the browser (client) and the server. During the handshake, the client requests a secure connection, and the server responds with its SSL/TLS certificate issued by a trusted Certificate Authority (CA). The certificate contains the server’s public key, which the client verifies to ensure authenticity—preventing impersonation or phishing attacks.
Once authenticated, both sides negotiate cryptographic parameters—such as the version of TLS and cipher suites—to define how encryption will work. The client then generates a random symmetric encryption key (called a session key) and encrypts it with the server’s public key. Only the server’s private key can decrypt it, ensuring the key exchange remains secure. This session key is used for fast two-way encrypted communication during the session.
After key exchange, the connection moves from handshake mode to encrypted data transmission mode. Now, every message is encrypted before sending and decrypted when received. TLS also includes mechanisms to verify that the data isn’t altered during transmission—this protects against Man-in-the-Middle (MITM) attacks and data tampering. If any suspicious modifications are detected, the connection is immediately terminated.
Together, TCP/IP ensures reliable delivery, while TLS ensures security. Without these technologies working hand-in-hand, secure e-commerce transactions, online banking, private messaging, and protected personal data exchange would not be possible. Today, nearly all major websites adopt HTTPS by default because user privacy and data security have become top priorities.
In summary, TCP/IP provides the underlying structure for communication, and TLS builds on top to ensure that communication is private and trusted. Understanding how both work together is essential for web developers, network engineers, and cybersecurity professionals, as they form the core of secure internet communication.
