Sandbox evasion techniques are methods used by malware to detect when it is being analyzed in a controlled environment and modify its behavior to avoid detection. Security sandboxes are commonly used by defenders to test suspicious files safely, so attackers design malware that appears harmless inside the sandbox but becomes active once executed on a real user’s machine. This makes threat detection more challenging for analysts and antivirus systems.
Malware may check for virtual machine signatures because many sandboxes run in virtualized environments like VMware or VirtualBox. It looks for known artifacts such as specific processes, registry keys, hardware properties, or lack of full device activity. If such markers are detected, malware may immediately terminate or delay execution to avoid inspection.
Sandbox evasion can also involve timing-based tricks. Some malware delays its malicious payload by sleeping for a long period, knowing that sandboxes usually have time limits for analysis. Advanced techniques include breaking sleep into tiny intervals or monitoring system clock manipulation to detect artificial fast-forwarding attempts by security tools.
Another evasion tactic is user interaction detection. Sandboxes often run automated and do not generate mouse movement, keyboard inputs, or touch interactions. Malware checks for natural human behaviors such as cursor movement patterns or window focus changes before activating harmful code. If no interaction is detected, it stays dormant.
Environmental checks help malware determine whether the system is real or controlled. These checks include scanning for small disk storage, low RAM capacity, unusual running processes, or missing installed applications. Sandboxes typically run minimal setups, which malware uses as signals to hide malicious operations.
Encrypted or obfuscated payload delivery is another advanced technique. Malware initially executes benign code but downloads or decrypts harmful components only after confirming it's outside a sandbox environment. This makes static analysis difficult because the malicious portion remains hidden during inspection.
Some malware interacts with hardware or network conditions to confirm authenticity. It checks internet connectivity, GPU availability, battery status, or even connected peripherals — factors often missing in sandbox environments. If expected hardware conditions are not found, malware refuses to execute fully.
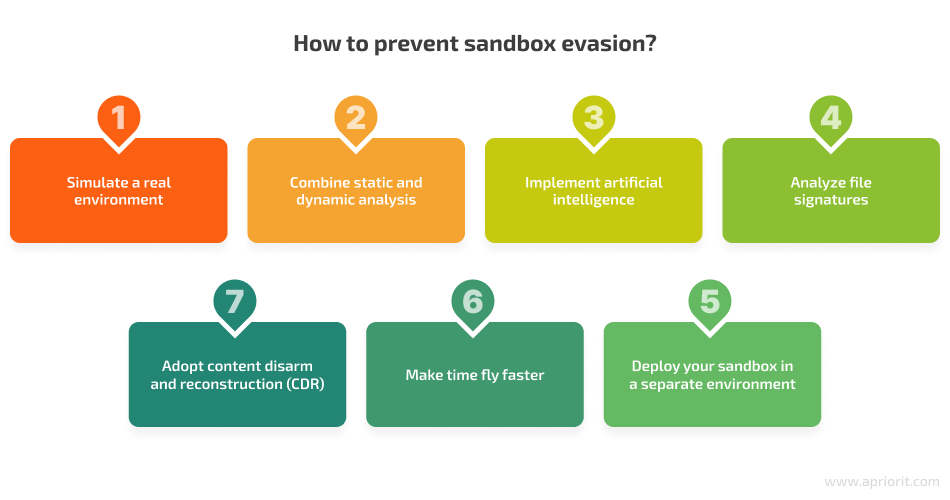
Evasion techniques continue evolving as cybersecurity systems become more advanced. AI-powered malware can dynamically learn sandbox detection patterns and adapt behavior to remain hidden. In response, sandbox technologies are improving realism — simulating human activity, enhancing system resources, and masking virtualization indicators.
In conclusion, sandbox evasion techniques highlight the ongoing battle between malware authors and security defenders. Understanding these tactics allows cybersecurity experts to improve analysis tools, reduce blind spots, and develop detection strategies that prevent malicious threats from escaping scrutiny and harming real systems.
Malware may check for virtual machine signatures because many sandboxes run in virtualized environments like VMware or VirtualBox. It looks for known artifacts such as specific processes, registry keys, hardware properties, or lack of full device activity. If such markers are detected, malware may immediately terminate or delay execution to avoid inspection.
Sandbox evasion can also involve timing-based tricks. Some malware delays its malicious payload by sleeping for a long period, knowing that sandboxes usually have time limits for analysis. Advanced techniques include breaking sleep into tiny intervals or monitoring system clock manipulation to detect artificial fast-forwarding attempts by security tools.
Another evasion tactic is user interaction detection. Sandboxes often run automated and do not generate mouse movement, keyboard inputs, or touch interactions. Malware checks for natural human behaviors such as cursor movement patterns or window focus changes before activating harmful code. If no interaction is detected, it stays dormant.
Environmental checks help malware determine whether the system is real or controlled. These checks include scanning for small disk storage, low RAM capacity, unusual running processes, or missing installed applications. Sandboxes typically run minimal setups, which malware uses as signals to hide malicious operations.
Encrypted or obfuscated payload delivery is another advanced technique. Malware initially executes benign code but downloads or decrypts harmful components only after confirming it's outside a sandbox environment. This makes static analysis difficult because the malicious portion remains hidden during inspection.
Some malware interacts with hardware or network conditions to confirm authenticity. It checks internet connectivity, GPU availability, battery status, or even connected peripherals — factors often missing in sandbox environments. If expected hardware conditions are not found, malware refuses to execute fully.
Evasion techniques continue evolving as cybersecurity systems become more advanced. AI-powered malware can dynamically learn sandbox detection patterns and adapt behavior to remain hidden. In response, sandbox technologies are improving realism — simulating human activity, enhancing system resources, and masking virtualization indicators.
In conclusion, sandbox evasion techniques highlight the ongoing battle between malware authors and security defenders. Understanding these tactics allows cybersecurity experts to improve analysis tools, reduce blind spots, and develop detection strategies that prevent malicious threats from escaping scrutiny and harming real systems.
