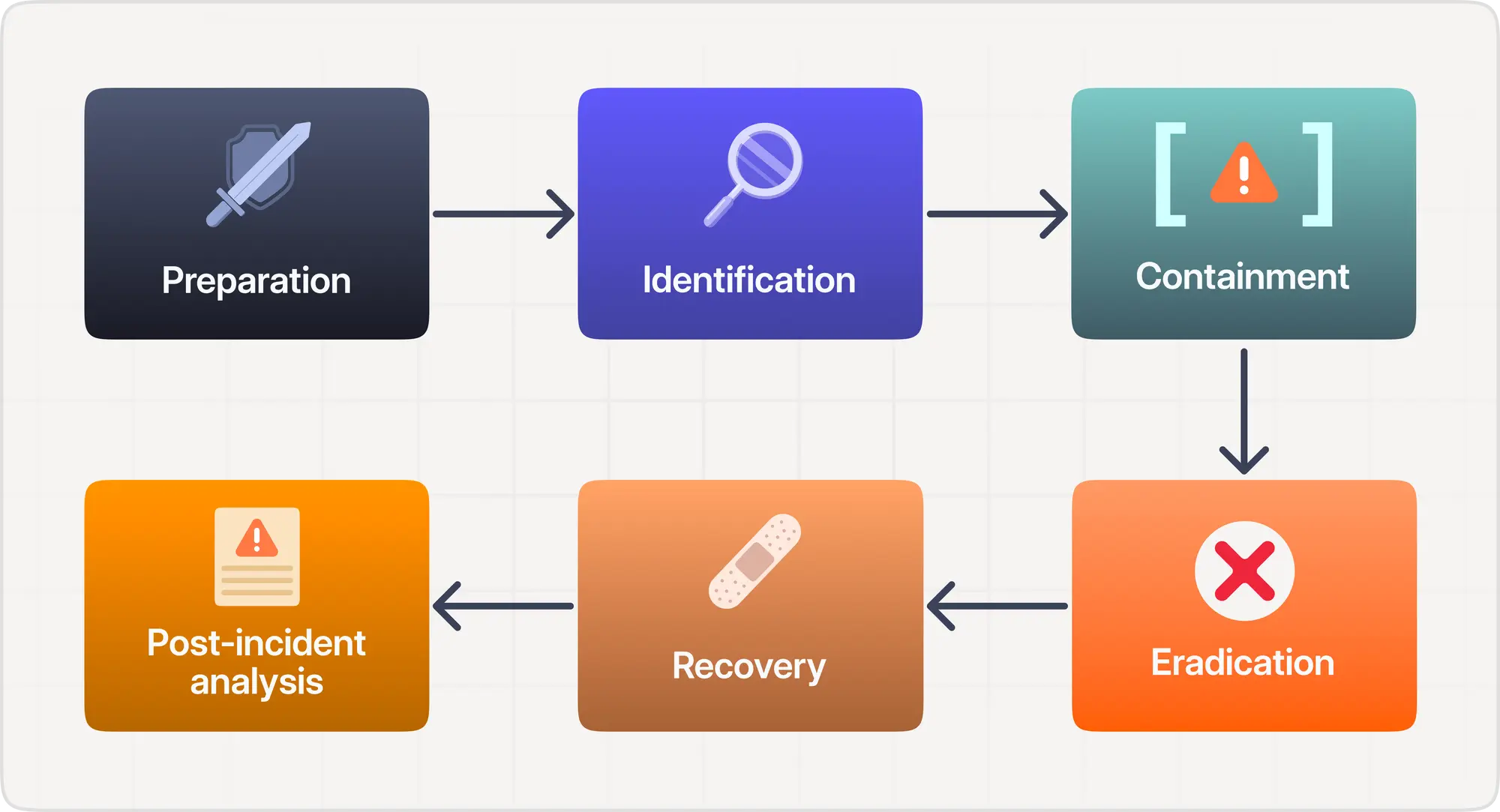
The Incident Response (IR) lifecycle is a structured approach to identifying, containing, and eliminating cybersecurity incidents. It ensures organizations respond quickly and systematically when attacks occur, minimizing damage and restoring normal operations. The lifecycle typically consists of six major phases: preparation, identification, containment, eradication, recovery, and lessons learned.
The preparation phase involves building the foundation of a strong IR plan. This includes defining roles, establishing communication channels, deploying monitoring tools, and setting up a trained incident response team. Proper preparation determines how effectively an organization handles real incidents.
The identification phase focuses on detecting suspicious behavior or confirmed attacks. Alerts from SIEM systems, anomaly detection, user reports, and automated monitoring tools help identify indicators of compromise. Analysts must analyze logs, validate alerts, and confirm whether an incident is genuine.
Once an incident is confirmed, containment becomes crucial. Containment techniques prevent attackers from spreading further or causing additional damage. Short-term containment may involve isolating infected systems, blocking IP addresses, or disabling compromised accounts. Long-term containment includes applying temporary fixes while preparing for full remediation.
The eradication phase removes the attacker and their artifacts completely. This step may involve deleting malicious files, removing backdoors, patching vulnerabilities, or rebuilding affected systems. Eradication ensures the attack cannot continue or reoccur.
Recovery focuses on restoring systems to normal operation while ensuring that no traces of the attack remain. This may include restoring clean backups, re-enabling services, and conducting additional monitoring. Recovery must be executed carefully to prevent immediate reinfection or operational issues.
The final phase, lessons learned, is critical but often ignored. After the incident is resolved, the team analyzes what happened, how it happened, what worked, and what failed. These insights improve future IR plans, strengthen defenses, and optimize communication processes within the organization.
Effective incident response requires coordination, documentation, and clear decision-making. Organizations that practice tabletop exercises and simulations respond faster and more confidently during real attacks.
The IR lifecycle transforms chaos into structured action. Organizations with mature IR processes recover quickly from attacks and maintain stronger resilience against cyber threats.
The preparation phase involves building the foundation of a strong IR plan. This includes defining roles, establishing communication channels, deploying monitoring tools, and setting up a trained incident response team. Proper preparation determines how effectively an organization handles real incidents.
The identification phase focuses on detecting suspicious behavior or confirmed attacks. Alerts from SIEM systems, anomaly detection, user reports, and automated monitoring tools help identify indicators of compromise. Analysts must analyze logs, validate alerts, and confirm whether an incident is genuine.
Once an incident is confirmed, containment becomes crucial. Containment techniques prevent attackers from spreading further or causing additional damage. Short-term containment may involve isolating infected systems, blocking IP addresses, or disabling compromised accounts. Long-term containment includes applying temporary fixes while preparing for full remediation.
The eradication phase removes the attacker and their artifacts completely. This step may involve deleting malicious files, removing backdoors, patching vulnerabilities, or rebuilding affected systems. Eradication ensures the attack cannot continue or reoccur.
Recovery focuses on restoring systems to normal operation while ensuring that no traces of the attack remain. This may include restoring clean backups, re-enabling services, and conducting additional monitoring. Recovery must be executed carefully to prevent immediate reinfection or operational issues.
The final phase, lessons learned, is critical but often ignored. After the incident is resolved, the team analyzes what happened, how it happened, what worked, and what failed. These insights improve future IR plans, strengthen defenses, and optimize communication processes within the organization.
Effective incident response requires coordination, documentation, and clear decision-making. Organizations that practice tabletop exercises and simulations respond faster and more confidently during real attacks.
The IR lifecycle transforms chaos into structured action. Organizations with mature IR processes recover quickly from attacks and maintain stronger resilience against cyber threats.
