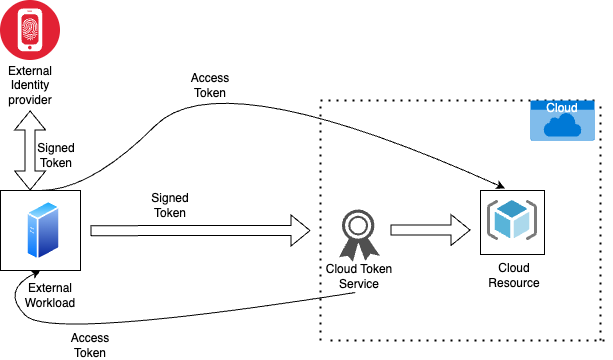
Cross-cloud identity federation allows users to authenticate across multiple cloud providers using a single identity system. This gives organizations flexibility, simplifies access, and reduces credential duplication. However, when identity becomes the central trust anchor across clouds, any compromise of identity services can lead to widespread and damaging breaches.
The primary risk lies in trust expansion. When multiple clouds rely on a single identity provider (IdP), an attacker who compromises authentication credentials or tokens can access assets in every connected environment. This creates a large blast radius — meaning one weak link can expose the entire cloud ecosystem.
A common threat scenario involves token theft. Tokens used in federation (like SAML assertions or OAuth JWTs) can be intercepted during transmission or collected from infected endpoints. Attackers can reuse stolen tokens to impersonate users without needing their passwords. The well-known SolarWinds breach showed how attackers leveraged token forgery to move laterally across cloud services.
Misconfiguration is another major issue. Policies, roles, and permissions must be consistently enforced across all clouds. But each cloud provider has different IAM models, making misalignment likely. Over-privileged access, unused roles, and weak conditional access policies can unintentionally grant attackers unauthorized privileges.
Supply chain dependency increases risk as well. Organizations rely on third-party apps integrated with identity federation — any vulnerability in these apps can serve as an entry point. Attackers often target SaaS applications connected to identity systems because they bypass traditional network defenses.
Monitoring becomes more complex in a federated environment. Logs are distributed across many platforms, making anomalies harder to detect. Lack of unified visibility leads to delayed detection and silent persistence, where attackers maintain long-term unauthorized access by rotating credentials, tokens, or app-based access.
To mitigate these risks, organizations enforce Zero Trust principles — verifying every user, device, and request continuously. Stronger MFA, token binding to devices, continuous authentication, and automated privilege revocation reduce exposure. Standardized governance ensures identity lifecycle policies are consistent across all cloud environments.
Compliance requirements also grow with federation. Businesses must track where identity data flows, who controls it, and how third parties handle it across borders. Data sovereignty laws add additional constraints when authentication data moves between jurisdictions.
In summary, cross-cloud identity federation delivers agility but significantly increases security complexity. Without robust controls, monitoring, and unified governance, attackers can exploit identity trust paths to access sensitive data in multiple clouds. As organizations expand cloud adoption, identity security becomes the cornerstone of multi-cloud resilience.
The primary risk lies in trust expansion. When multiple clouds rely on a single identity provider (IdP), an attacker who compromises authentication credentials or tokens can access assets in every connected environment. This creates a large blast radius — meaning one weak link can expose the entire cloud ecosystem.
A common threat scenario involves token theft. Tokens used in federation (like SAML assertions or OAuth JWTs) can be intercepted during transmission or collected from infected endpoints. Attackers can reuse stolen tokens to impersonate users without needing their passwords. The well-known SolarWinds breach showed how attackers leveraged token forgery to move laterally across cloud services.
Misconfiguration is another major issue. Policies, roles, and permissions must be consistently enforced across all clouds. But each cloud provider has different IAM models, making misalignment likely. Over-privileged access, unused roles, and weak conditional access policies can unintentionally grant attackers unauthorized privileges.
Supply chain dependency increases risk as well. Organizations rely on third-party apps integrated with identity federation — any vulnerability in these apps can serve as an entry point. Attackers often target SaaS applications connected to identity systems because they bypass traditional network defenses.
Monitoring becomes more complex in a federated environment. Logs are distributed across many platforms, making anomalies harder to detect. Lack of unified visibility leads to delayed detection and silent persistence, where attackers maintain long-term unauthorized access by rotating credentials, tokens, or app-based access.
To mitigate these risks, organizations enforce Zero Trust principles — verifying every user, device, and request continuously. Stronger MFA, token binding to devices, continuous authentication, and automated privilege revocation reduce exposure. Standardized governance ensures identity lifecycle policies are consistent across all cloud environments.
Compliance requirements also grow with federation. Businesses must track where identity data flows, who controls it, and how third parties handle it across borders. Data sovereignty laws add additional constraints when authentication data moves between jurisdictions.
In summary, cross-cloud identity federation delivers agility but significantly increases security complexity. Without robust controls, monitoring, and unified governance, attackers can exploit identity trust paths to access sensitive data in multiple clouds. As organizations expand cloud adoption, identity security becomes the cornerstone of multi-cloud resilience.
